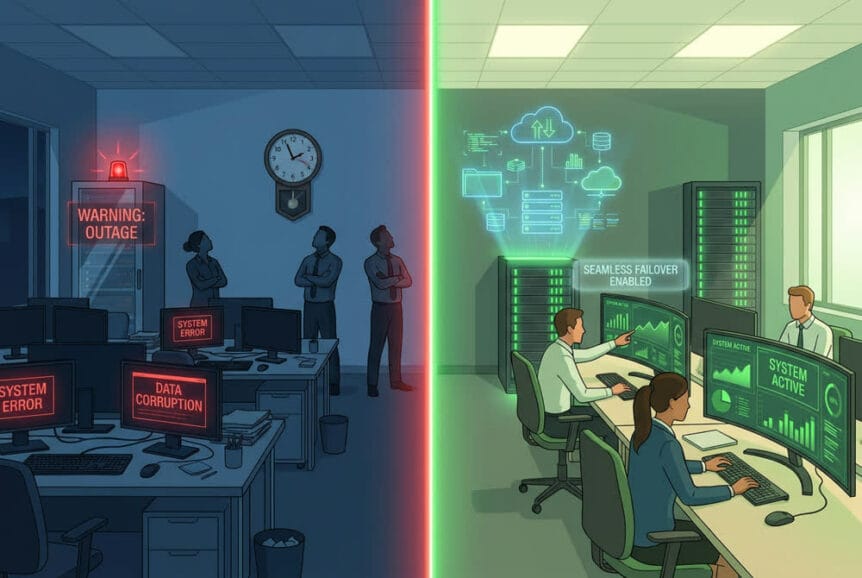
The Critical Gap Between Data Backup and Business Continuity Most business owners believe their data backup system provides complete protection against disasters. This assumption creates a dangerous blind spot: while your data might be safely stored, your business operations can still grind to a halt for hours or even days …
How AI-Powered Phishing Attacks Are Forcing Businesses to Rethink Email Security in 2026
The cybersecurity landscape has undergone a fundamental transformation. Cybercriminals now wield generative AI tools that produce flawless phishing emails in multiple languages, completely eliminating the traditional red flags that security professionals have taught employees to watch for over the past two decades. The numbers tell a stark story. Since ChatGPT’s …
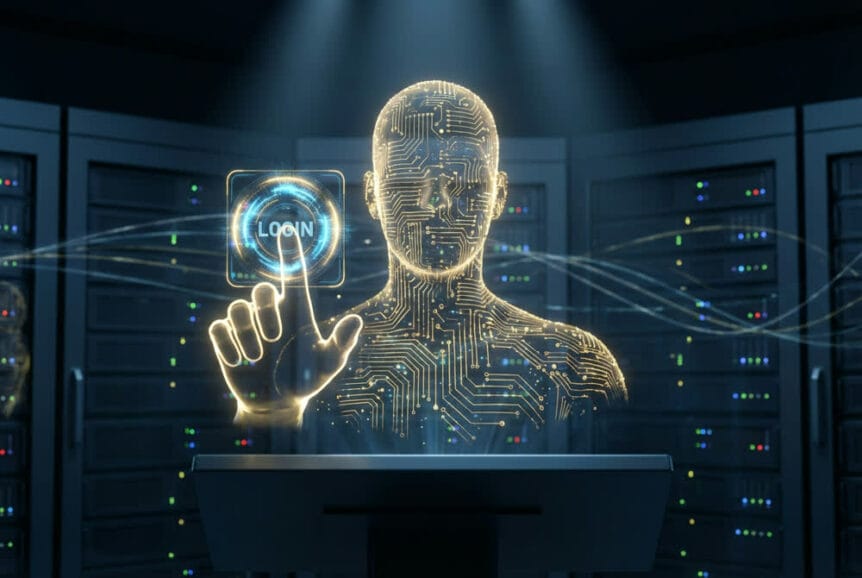
Identity Management: The New Cybersecurity Battleground Every Business Must Defend
Why Identity Has Become the Primary Target for Cybercriminals Cybercriminals have fundamentally changed their approach to breaching business networks. Rather than spending weeks searching for software vulnerabilities or attempting to break through firewalls, attackers now prefer a simpler path: they use stolen credentials to walk right through the front door. …
Your AI Assistant Can Be Tricked Just Like Your Human Assistant: Why Digital Vigilance Matters More Than Ever
Your executive assistant receives an urgent email from someone claiming to be the CEO, requesting an immediate wire transfer. The language sounds right, the timing creates pressure, and the request comes through official channels. Your assistant, wanting to be helpful and responsive, nearly complies before double-checking. This scenario plays out …
FCC Bans Foreign-Made Consumer Routers: What Your Business Needs to Know
On March 23, 2026, the Federal Communications Commission added all new foreign-manufactured consumer-grade routers to its Covered List, effectively prohibiting them from receiving the equipment authorization required for importation, marketing, and sale in the United States. The decision followed a March 20, 2026 National Security Determination issued by a White …
Protecting Your Business from Identity Theft and Refund Fraud in 2026
Tax season has always attracted opportunistic criminals, but the scale and sophistication of attacks in 2026 represent a significant escalation. The IRS Criminal Investigation division reported a 111.8% surge in identified tax fraud during fiscal year 2025, with total fraud reaching $4.5 billion. Meanwhile, the Federal Trade Commission logged nearly …
OpenClaw Security Alert: Critical Risks Every Business Must Know About This AI Agent
What Is OpenClaw and Why Should Your Business Care OpenClaw is not a chatbot. That distinction matters more than it might initially seem. Unlike a standard AI assistant that waits for a question and returns an answer, OpenClaw is an autonomous AI agent, meaning it operates continuously, makes decisions independently, …
How AI-Generated Fake Websites Are Fooling Employees
The New Reality: AI Can Clone Any Website in Minutes Building a convincing fake website used to require real technical skill. A scammer needed to know HTML, CSS, and web design well enough to fool a cautious visitor. That barrier is gone. Today, anyone with a browser and a few …
When Robot Vacuums Attack: The Hilariously Terrifying Reality of Hacked Smart Home Devices
The Weekend Project That Accidentally Hacked 7,000 Homes Some of the most consequential cybersecurity discoveries in recent history have come not from well-funded research labs, but from curious hobbyists with too much free time and a good idea. The story of Sammy Azdoufal and his DJI Romo robot vacuum is …
Executive Award Scams: How Cybercriminals Use Fake Recognition Programs to Steal Credentials and Deploy Malware
The Rise of Executive-Targeted Award Scams A sophisticated phishing campaign uncovered by Trustwave SpiderLabs researchers is making the rounds, and it is specifically designed to fool senior executives. The scheme impersonates the prestigious luxury brand Cartier, presenting targets with a fabricated “Cartier Recognition Program” that promises exclusive professional recognition. This …