US telecommunications giant T-Mobile is the latest big company to suffer from a successful hacking attack. The company is still cooperating with law enforcement and investigating an attack. Here are the details. A threat actor claimed to have made copies of databases that contained personal information belonging to more than …
Microsoft 365 Getting Button To Easily Report Phishing Emails
We’re beginning to see increasing collaboration between giant tech companies and government agencies around the world. In the UK the National Cyber Security Centre (NCSC) launched its Suspicious Email Reporting Service (SERS) back in April of 2020. The agency has received nearly 7 million reports since its launch. These include …
End to End Encryption Comes Facebook Messenger
Facebook has recently announced an important addition to its Facebook Messenger app. Most popular communications platforms utilize end-to-end encryption (E2EE). These include Zoom, Microsoft Teams, and even Facebook’s WhatsApp. Until recently Facebook’s Messenger app was a notable holdout. Although popular it simply wasn’t as secure as the others mentioned above. …
Change Your NAS Device Password To Avoid Ransomware Attacks
A NAS manufacturer based in Taiwan called Synology recently issued a warning to its customers relating to the StealthWorker botnet. This botnet has been targeting a wide range of NAS (Network Attached Storage) devices using simple brute force tactics. Anytime the botnet succeeds in breaching the security of a NAS …
Coalition Of Big Names Coming Together To Fight Ransomware
If you’re worried about ransomware attacks know that help is on the way. The CISA (Cybersecurity & Infrastructure Security Agency) has announced a partnership with some of the biggest names in tech. The specific purpose of this collaborative effort called the Joint Cyber Defense Collaborative is to put an end …
Even Computer Hardware Manufacturers Can Get Hit By Ransomware
Retailers, hospitals and financial institutions tend to be the targets of choice for the hackers of the world. Of course they’re not the only targets. The simple truth is that any company can find itself in the cross hairs of a hacker. The most recent victim is Taiwanese motherboard manufacturer …
Google Working On One Tap Solution To Password Issue
Internet users are notoriously bad at selecting secure passwords for the sites they frequently use that require a login. Surveys reveal that more than a third of internet users are in the habit of using the same password across multiple sites. The danger is that if a hacker breaches one …
Hackers Offering Fake Free Kindle Ebooks To Hack Amazon Accounts
Do you own an Amazon Kindle? Amazon has a warning for you if you do. Beware. Hackers are now using poisoned ebooks to delete the contents of infected Kindle readers and take control of a victim’s Amazon account. The hackers take advantage of the fact that on any given day …
New Stalkerware Tracks The Location Of Its Victims
A startling revelation was made at the recent Black Hat cybersecurity conference in Las Vegas, Nevada. The ongoing pandemic has given rise to a new threat named Stalkerware. It is defined as apps (both malicious and mundane) that are being used increasingly to coerce and control individuals. Stalkerware is used …
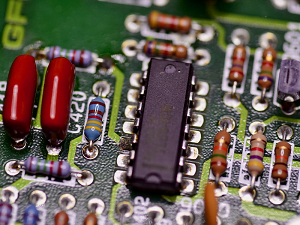
Older Industrial Technology May Have Security Risks
The vulnerability of Industrial Control Systems has been getting a lot of press in recent months. That’s a good thing because most people don’t spend much time thinking or worrying about such systems. Unfortunately they are among the most vulnerable systems of all. Industrial Control Systems haven’t really changed all …