Scammers will use anything to target businesses, including tax forms. A new phishing campaign is spreading a malicious program disguised as documents from the IRS. With the tax season in full swing soon, business owners must take extra precautions to protect sensitive company data. Emotet Phishing Campaign Targets Taxpayers Emotet …
Using Technology to Improve Employee Productivity
It is crucial to make the most of available technology to stay ahead of the competition in today’s fast-paced business environment. As a result, business owners are always searching for ways to increase efficiency and employee productivity. Here are some tips and strategies for using technology to boost employee productivity. …
How Cybercriminals are Exploiting the Silicon Valley Bank Shutdown
Recently, there was a rise in cybercrimes related to the closing of Silicon Valley Bank (SVB). Threat actors go after businesses and sometimes use them in their illegal activities. SVB was the 16th largest bank in the U.S. The bank worked with tech giants like Buzzfeed, Roblox, and Roku. However, …
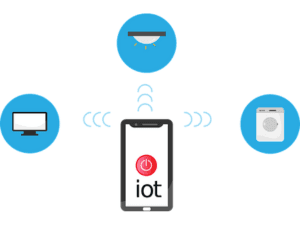
Harnessing the Power of the Internet of Things (IoT) for Business
You may have heard the term Internet of Things (IoT) as a business owner. But are you aware of its extent and how it can benefit your company? IoT is all about connecting everyday objects with sensors, software, and technology. This allows them to “talk” to each other over the …
SAP Releases Patches for Various Flaws
SAP, a leading business software company, recently released fixes for 19 bugs in its products. Hackers could delete files, add code, or access sensitive data through some of these flaws. Four flaws have high severity, while 10 have a medium severity rating. Understanding the SAP Vulnerabilities SAP products that …
Bitwarden’s Iframe Flaw Explained
The purpose of password managers is to safeguard our login credentials and online accounts. However, a popular password manager recently made headlines for its major security flaw. Bitwarden is under scrutiny because its autofill feature gives hackers easy access to sensitive information. The company has known about the vulnerability for …
Everything to Know About Essendant’s Multi-Day Outage
Essendant, a Staples-owned wholesale distributor of office supplies and stationery, paused its operations recently because of a multi-day, network-wide outage. The system disruption has prevented customers from placing orders online or contacting the company’s customer care unit. While Essendant has yet to disclose the reason behind the outage, many think …
Hiatus Malware Targets Business Routers
There is a new malware campaign targeting business-grade routers. It is called Hiatus, a complex operation that deploys the HiatusRAT malware. It is a kind of Remote Access Trojan (RAT) that cybercriminals use to gain remote control over a target system. Hiatus is the first of its kind. Lumen’s security …
Reduce the Risk of Business Email Compromise Attacks
Email threats have been around since the early 90s. But phishing techniques are much more sophisticated now than they were back then. One of the most successful and lucrative tactics is business email compromise (BEC). BEC scams have stolen over $43 billion from businesses worldwide between July 2019 and December …
Hatch Bank Falls Victim to Data Breach
Hatch Bank confirmed a data breach that compromised its customers’ personal data. The financial technology firm said hackers found a vulnerability in its internal file-transfer software. This allowed the hackers to access and steal around 140,000 customer names and social security numbers from Jan. 30-31, 2023. Hatch is using Fortra’s …