Learn how hackers are exploiting Microsoft Sway with malicious QR codes and discover essential preventive measures to safeguard your digital environment.
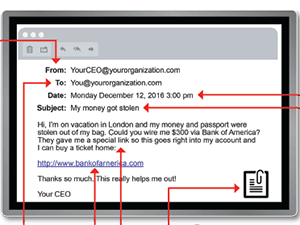
How To Recognize The Phishing Clues
In recognition of Cybersecurity Awareness Month, we wanted to share this guide for spotting a phishing email. The best way to avoid falling for phishing emails and clicking where you shouldn’t is to recognize the red flags. We recommend printing this guide and keeping it handy so you can spot …
Quick Take On Keeping Your Mobile Devices Secure
As remote work and connecting while traveling has become the norm, mobile device security responsibilities have also increased. We take our smartphones, tablets and laptops to airports, cafes and other public places, so the threat of a cyber attack targeting our devices is constant. There are some best practices to …
Critical Security Flaws in Microsoft Apps on MacOS
Discover the critical security flaws in Microsoft apps on MacOS that allow hackers to access sensitive data. Get practical tips to safeguard your system now.
Protect Your Business from Advanced Info Stealer Malware
Discover how to safeguard your organization’s sensitive data from sophisticated malware campaigns. Learn effective strategies for email security, staff education, and comprehensive security tools.
Protect Your Business from EDRKillShifter Malware
EDRKillShifter malware neutralizes EDR systems, leaving businesses vulnerable. Learn essential strategies to protect your organization from this rising cyber threat.
Enhance Business Security with Effective Cybersecurity Practices
Learn essential cybersecurity strategies like employee training, multi-factor authentication, and patch management to protect your business from cyber threats.
Combatting Social Engineering and FakeBat Loader Malware
Discover how social engineering and FakeBat Loader malware work, and learn best practices for protecting your business from these advanced cyber threats.
Election-Themed Scams Are on the Rise
Researchers at Malwarebytes warn of a surge in election-themed scams ahead of November’s presidential election in the US. These attacks can be expected to increase as the election grows closer. “The lure that we have seen the most involves asking people to donate to a campaign,” Malwarebytes says. “Whether that …
Protect Your Business with Timely Software Updates
Learn why regular software updates are vital for cybersecurity, performance, and device compatibility. Keep your business secure and efficient by prioritizing updates.